Похожее видео
HackTheBox - Backdoor
Видео: HackTheBox - Backdoor
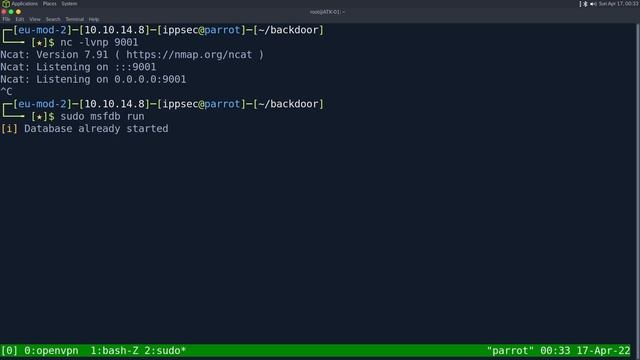
00:00 - Intro 00:50 - Start of nmap 02:10 - Starting WPSCAN 02:50 - Theres no index.php in wp-contentplugins which lets us find a vulnerable plugin eBook Download 1.1 05:50 - Playing with the eBook Download LFI 07:45 - Doing a full nmap portscan 08:20 - Using the LFI to extract the process names with curling proc and doing some cutsed magic 10:15 - Downloading the cmdline for the first 1000 PIDs 13:00 - Using find to show us files greater than a couple bytes to show us every valid PID 14:40 - Examining the final output discovering screen running and gdb 16:00 - Using metasploit to exploit GDB 21:50 - Reverse shell returned playing with screen to connect to the session 24:30 - Attaching to the root session then digging into why this worked 31:40 - Digging into wpscan to see how to make it find this,