Похожее видео
Splunk SIEM Security Training
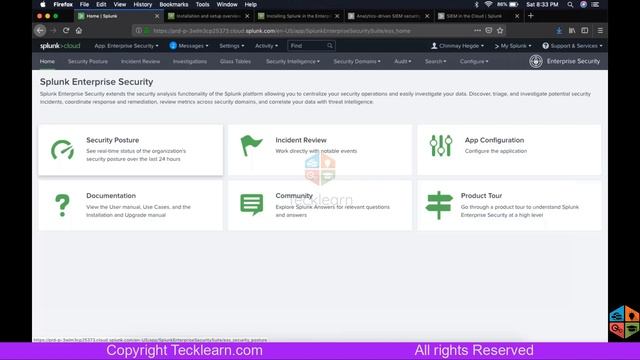
Видео: Splunk SIEM Security Training
Splunk SIEM Security Information and Event Management training is an industry-designed course for gaining expertise in Splunk Enterprise Security ES. Splunk Security Intelligence and Enterprise Management is a top tool for enterprise security management and event management. As part of this training you will learn how to deploy Splunk SIEM for investigating monitoring and deploying security solutions. You will get an in-depth knowledge of these concepts and will be able to work on related demos. Upon completion of this online training you will hold a solid understanding and hands-on experience with Splunk SIEM. Why you take Splunk SIEM Security Training? The average salary for an Information Security Analyst with Splunk skills is 105000. PayScale.com Splunk SIEM combines patterns machine learning and threat intelligence to verify all instances within a network. It offers greater scalability to help with network monitoring and works easily with other tools to improve defences. Curriculum Introduction to Splunk Security Splunk security Fundamentals Traditional security threats Concept of Security Data model Describing correlation searches Investigation and Monitoring Monitor the dashboard Investigating of notable events using incident review dashboards Workflow investigation and relative actions on identified flow Investigations Enterprise Security Model Managing Visualizing and Coordinating incident investigations using Deployment of ES investigation timelines Using journals and timelines for documenting breach analysis Efforts required to mitigate the issues Security Posture Incident Review Risk Analysis and Network Analysis Risk analysis and identification Risk dashboard utilization How to manage the risk scores for objects and users Network Analysis Web Intelligence HTTP category analysis HTTP user agent analysis Analyzing traffic size for spotting new threats About the Splunk Enterprise Security Framework Spam Assassin Architecture Email Filter Architecture ES Solution Architecture Various Templates Threat Intelligence Inspecting threat intelligence content with threat artefact dashboard Monitoring malicious websites with threat activity dashboard User Intelligence Anomaly dashboards for user role and access logs Identity and asset concepts Creating and tuning correlation searches Implementing the add-ons with Splunk Using the Various Features of SIEM Deploying Splunk Security Framework on AWS ,